The Injection Pipeline
Open a handle to the target process, allocate memory inside it, write your payload, then trigger execution. Each step has multiple techniques with different stealth profiles.
Loaders and injectors are the delivery mechanism for game cheats. They get your DLL or shellcode into a target process. Understanding injection techniques is fundamental to both cheat development and anti‑cheat research.
Open a handle to the target process, allocate memory inside it, write your payload, then trigger execution. Each step has multiple techniques with different stealth profiles.
The simplest method: allocate a string in the target, then create a remote thread calling LoadLibrary with your DLL path. Easy to implement, easy to detect.
Parse the PE file yourself, map sections, resolve imports, and call the entry point — all without the module appearing in the loaded module list. Much stealthier than LoadLibrary.
The classic API for starting a thread in another process. Straightforward but heavily monitored by anti‑cheats. Often the first method beginners learn.
Suspend an existing thread in the target, modify its instruction pointer to run your code, then resume it. Avoids creating a new thread, which is a common detection vector.
The DLL maps itself into memory using a small bootstrap loader embedded in the PE. No external injector needed after the initial code execution — common in advanced loaders.
This rewrite explains what the GamerFun Valorant Menu v4 actually is, how its Python .exe workflow…

Unlock All Skins, Camos, and Levels in Call of Duty: Warzone, Cold War & Modern Warfare…

Many players search for CrossFire PH hacks for ESP, aimbot, and no recoil, but most pages…
⚠️ Malware Warning: Injectors use the same techniques as malware. Never run untrusted loaders — they may contain backdoors, keyloggers, or miners. Build from source you’ve audited, or study existing open‑source injectors.
They're often used interchangeably. Technically, an injector puts code into a process, while a loader may also handle authentication, updates, and payload decryption before injecting. Most cheat "loaders" are injectors with extra features.
For stealth, yes — manual mapping doesn't register the DLL in the process's module list, making it harder for anti-cheats to find. But it's significantly more complex to implement correctly, especially with TLS callbacks and exception handling.
Yes. Kernel anti-cheats can scan for executable memory regions that don't correspond to any loaded module (a sign of manual mapping). They can also monitor VirtualAllocEx and NtWriteVirtualMemory calls.
For learning, absolutely — it teaches you PE format, process internals, and Windows APIs. For actual use, never trust injectors you didn't build or audit yourself. Malicious injectors are extremely common in the cheat scene.
This rewrite breaks down what PhasmoMenu by PappyG actually does, how its .EXE workflow works, and where players usually run into trouble. It also covers the part most guides dodge: Terms of Service, platform limits, version breakage, and why testing discipline matters.
DayZ 1.26 cheats usually mean third-party PC tools that expose ESP, aimbot, freecam, loot highlighting, and visibility tweaks. This rewrite keeps the original feature set intact while adding the anti-cheat reality, patch-compatibility context, and file-safety guidance most pages skip.
This rewrite keeps the original Vigor internal DLL workflow intact and explains it in a cleaner, more useful format. You’ll get the exact setup path, feature coverage, troubleshooting, and realistic risk notes without the usual spammy fluff.
FSL is usually described as a Fast Save Loader workflow for GTA 5 on PC that relies on a version.dll drop-in and local save handling. This rewrite explains what it actually does, where people get confused, and why ban risk and platform limits matter before you test anything.
This rewrite breaks down what the 4u4play Fortnite PC cheat actually includes, how its setup flow works, and where the real detection and malware risks start. It keeps the original feature list intact while adding the anti-cheat context most download pages leave out.
Many players search for CrossFire PH hacks for ESP, aimbot, and no recoil, but most pages skip the part that actually matters: detection, bans, and malware risk. This outline reframes the topic from a reverse engineer’s perspective so readers understand what these tools are, why they get flagged, and what warning signs to watch before they click anything.
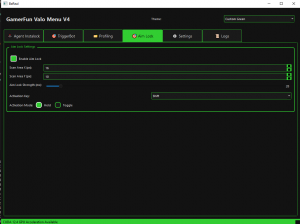
This rewrite explains what the GamerFun Valorant Menu v4 actually is, how its Python .exe workflow functions, and where triggerbot, aimlock, and insta lock fit technically. It also covers the part most pages dodge: Riot Vanguard risk, bad assumptions about AHK, and what to avoid before testing anything.
Blox Fruits hacks are usually Lua scripts loaded through a Roblox executor, not magic cheat codes. This rewrite keeps the original script pack intact while explaining what the scripts do, how setup works, and where people get banned or burned by fake loaders.
This rewrite explains the same Python-based external TensorRT aimbot and triggerbot from GamerFun without the usual hype. You’ll get the setup flow, feature breakdown, platform limits, and the real detection and malware risks before testing anything.
Not every MM2 script is good at the same job. This outline compares hub types, feature sets, compatibility, and ban risk from a reverse-engineering angle instead of pretending any script is permanently working or safe.