Memory Reading
Use ReadProcessMemory (Windows API) or libraries like pymem / pymeow to read game values — health, coordinates, entity lists — from a separate process.
External cheats operate outside the game process, using OS‑level APIs to read and write memory. They’re easier to develop than internals and a natural next step after mastering Cheat Engine basics.
Use ReadProcessMemory (Windows API) or libraries like pymem / pymeow to read game values — health, coordinates, entity lists — from a separate process.
Modify game state externally with WriteProcessMemory. Freeze health, set ammo, or teleport — all without injecting code into the game.
Draw ESP boxes, health bars, and radar on a transparent window layered over the game. Common in Python and C# external cheats.
The fastest way to prototype an external cheat. Read/write memory in a few lines of Python. Great for learning before moving to C++.
Higher performance external cheats using raw WinAPI calls. Better for real‑time ESP and aimbot where Python’s overhead is noticeable.
AutoHotKey scripts for input automation — recoil control, rapid fire, or movement macros. Lightweight but effective for specific use cases.
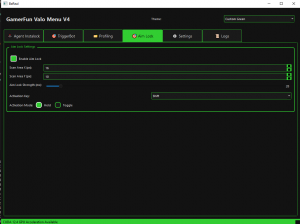
This rewrite explains what the GamerFun Valorant Menu v4 actually is, how its Python .exe workflow…

Unlock Your Potential: A Comprehensive Guide to Overwatch 2 Cheats (AIM & ESP) in 2025 The…

Download Kernel Warzone Free External ESP Cheat: Aimbot, Bone ESP, More for 2025 – Safe &…
⚠️ Detection Note: External cheats are not invisible. Modern anti‑cheats scan for open process handles, suspicious overlays, and known tool signatures. Always test in offline or private environments.
They're generally easier to develop and slightly harder for basic anti-cheats to detect, but modern kernel-level anti-cheats (EAC, BattlEye, Vanguard) detect external reads just as effectively. Neither is "safe" in online games.
Python with pymem for prototyping and learning. C++ for production-quality tools where performance matters. C# is a solid middle ground with good WinAPI bindings.
Yes — you read entity positions from game memory, project them to screen coordinates using the view matrix, then draw on a transparent overlay window. Python (pygame/tkinter) or C++ (DirectX) both work.
A Windows API function that lets one process read the memory of another process. It's the foundation of all external cheats — you pass a process handle, an address, and a buffer to receive the data.
LSCHaX is an external GTA V vehicle-editing workflow tied to Los Santos Customs, not a generic DLL menu or injector. This outline keeps the original feature set and usage flow, then adds the missing 2026 context around build support, ban risk, malware screening, and troubleshooting.
This rewrite explains what the original external Sea of Thieves ESP tool claims to offer, how its .exe setup flow works, and where the real risks usually show up. It keeps the original feature set intact while adding current-year context, anti-cheat caution, and practical troubleshooting.
Reverse engineering anti-cheat research is about understanding how modern game protection systems observe, verify, and flag suspicious behavior. This outline builds a research-first article for 2026 that explains architecture, workflow, legal boundaries, and comparison points without turning into a bypass guide.
Bodycam players usually ask one thing first: does the game have anti-cheat, and what happens if you test ESP or aimbot features anyway? This rewrite keeps the original cheat feature set intact, but reframes it around detection reality, update fragility, and lower-risk alternatives in 2026.
This outline rewrites the original Black Ops 6 Python AFK bot article without changing the tool itself: a Python script using Tesseract OCR and simulated inputs. It adds a cleaner 2026 structure, honest ban-risk coverage, setup flow, and troubleshooting notes that advanced readers actually need.
DarkyyWare is a Roblox KAT Lua script hub built around combat-assist, movement, and utility toggles like Silent Aim, Kill Aura, and Trigger Bot. This outline keeps the original feature set and usage flow, then adds the missing context most pages skip: compatibility, remote-loader risk, troubleshooting, and honest ToS exposure.
This rewrite keeps the original Blade Ball mobile script roundup intact, but adds the context most pages skip: feature analysis, mobile compatibility, and realistic risk notes. You’ll get a cleaner 2026 comparison of script types, setup workflow, and what to avoid before testing anything.
This rewrite keeps the same Combat Master internal DLL cheat, injector workflow, and original feature set, but updates the guidance for 2026. It also adds the part most thin pages skip: realistic setup limits, known issues, and ban-risk context from a reverse-engineering angle.
Marvel Rivals colorbots sit in a weird spot: lower visibility than many internal cheats, but still risky and still against ToS. This outline frames the tool honestly, explains the Arduino and GHUB paths, and shows why patches, lighting, and input methods make or break it.
Cheating, injected tools, and unauthorized mods can get your Marvel Rivals account flagged or banned, and appeal success usually depends on evidence, not emotion. This outline breaks down what likely carries the most risk, what HWID rumors actually mean, and how to handle a false ban responsibly.