Hardware Fingerprinting
Games and anti‑cheats collect unique identifiers from your CPU, GPU, motherboard, disks, network adapters, and Windows installation to build a hardware profile.
Hardware ID (HWID) bans tie a ban to your physical hardware rather than just an account. Understand how games fingerprint your machine, what identifiers they collect, and how the research community studies these systems.
Games and anti‑cheats collect unique identifiers from your CPU, GPU, motherboard, disks, network adapters, and Windows installation to build a hardware profile.
Unlike account bans, HWID bans persist across new accounts. If your hardware fingerprint matches a banned profile, you’re blocked before you even log in.
Common vectors: disk serial numbers, motherboard UUID, MAC addresses, GPU serial, Windows Machine GUID, TPM data, and SMBIOS tables.
NVMe/SATA serial numbers are one of the most common HWID sources. They’re unique to each drive and easy for anti‑cheats to query via WMI or DeviceIoControl.
MAC addresses and adapter GUIDs provide network‑level fingerprinting. Some anti‑cheats also check adapter names and driver versions.
Machine GUID, product ID, computer SID, and registry‑stored installation data all contribute to the fingerprint. Reinstalling Windows alone often isn’t enough.

Free Valorant Triggerbot Hack | 2025 Undetectable & Safe Looking to elevate your performance in Valorant…
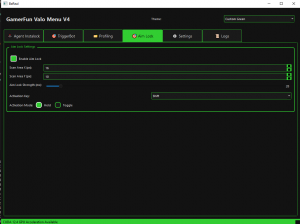
This rewrite explains what the GamerFun Valorant Menu v4 actually is, how its Python .exe workflow…

Unlock the Ultimate Heist with Payday 3 Always Glow Cheat Engine Table – Download Now on…
⚠️ Legal & Ethical Note: HWID spoofing to evade bans violates virtually every game’s Terms of Service and may violate computer fraud laws in some jurisdictions. These articles are for educational research only — understanding how systems work, not circumventing them.
It's rare but possible. Most HWID bans come from online multiplayer anti-cheats (EAC, BattlEye, Vanguard, RICOCHET). Single-player games rarely implement hardware fingerprinting.
Usually not. Anti-cheats collect multiple identifiers and use fuzzy matching — changing just your disk or MAC address may not be enough if other components still match the banned profile.
A tool that intercepts the system calls anti-cheats use to read hardware identifiers and returns fake values. They typically run at kernel level (as drivers) to intercept low-level queries. They're studied for research purposes.
Spoofing itself isn't illegal in most jurisdictions, but using it to circumvent bans violates Terms of Service (a contract). In some cases it could intersect with computer fraud statutes. This is not legal advice — consult a professional.
This rewrite breaks down what PhasmoMenu by PappyG actually does, how its .EXE workflow works, and where players usually run into trouble. It also covers the part most guides dodge: Terms of Service, platform limits, version breakage, and why testing discipline matters.
DayZ 1.26 cheats usually mean third-party PC tools that expose ESP, aimbot, freecam, loot highlighting, and visibility tweaks. This rewrite keeps the original feature set intact while adding the anti-cheat reality, patch-compatibility context, and file-safety guidance most pages skip.
This rewrite keeps the original Vigor internal DLL workflow intact and explains it in a cleaner, more useful format. You’ll get the exact setup path, feature coverage, troubleshooting, and realistic risk notes without the usual spammy fluff.
FSL is usually described as a Fast Save Loader workflow for GTA 5 on PC that relies on a version.dll drop-in and local save handling. This rewrite explains what it actually does, where people get confused, and why ban risk and platform limits matter before you test anything.
This rewrite breaks down what the 4u4play Fortnite PC cheat actually includes, how its setup flow works, and where the real detection and malware risks start. It keeps the original feature list intact while adding the anti-cheat context most download pages leave out.
Many players search for CrossFire PH hacks for ESP, aimbot, and no recoil, but most pages skip the part that actually matters: detection, bans, and malware risk. This outline reframes the topic from a reverse engineer’s perspective so readers understand what these tools are, why they get flagged, and what warning signs to watch before they click anything.
This rewrite explains what the GamerFun Valorant Menu v4 actually is, how its Python .exe workflow functions, and where triggerbot, aimlock, and insta lock fit technically. It also covers the part most pages dodge: Riot Vanguard risk, bad assumptions about AHK, and what to avoid before testing anything.
Blox Fruits hacks are usually Lua scripts loaded through a Roblox executor, not magic cheat codes. This rewrite keeps the original script pack intact while explaining what the scripts do, how setup works, and where people get banned or burned by fake loaders.
This rewrite explains the same Python-based external TensorRT aimbot and triggerbot from GamerFun without the usual hype. You’ll get the setup flow, feature breakdown, platform limits, and the real detection and malware risks before testing anything.
Not every MM2 script is good at the same job. This outline compares hub types, feature sets, compatibility, and ban risk from a reverse-engineering angle instead of pretending any script is permanently working or safe.